Ransomware list incl. Decryptor (for decryption)
With our ransomware list, you can identify ransomware Trojans and decrypt them if necessary. If a decryption program is available, we will provide you with the appropriate program for download..
To identify ransomware, you need two things: the file name of the ransom note (e.g. HELP_DECRYPT.TXT), and the file extension of the encrypted files (e.g. .encrypt).
Our ransomware list ↓ currently contains 469 ransomware variants and documents the file extensions + ransom note used in each case. Where available, there are links to Decryptor (for decryption).
Decrypt ransomware: list of decryption tools
Wichtig: Bevor man entschlossen, aber halbwissend zur Selbsthilfe schreitet und den Ransomware-Schaden womöglich noch vergrößert, sollte man eine Datensicherung der verschlüsselten Dateien anlegen.
| Ransomware | Extensions | Ransom Note Filename | Comment | Encryption Algorithm | Decryptor |
|---|---|---|---|---|---|
| $ ucyLocker | .WINDOWS | READ_IT.txt | |||
| .CryptoHasYou. | .enc | YOUR_FILES_ARE_LOCKE |
AES (256) | ||
| 010001 | .010001 | tmpsfn_as.txt | 500 $ Lösegeld in Bitcoin. E-Mail-Adresse:
jduy3jd87dhs@grr.l |
AES | |
| 05250lock | .random(5) | XXXXXXXX-FILES ENCRYPTED.txt |
E-Mail-Adressen:
05250lock@tutamail |
AES | |
| 0kilobypt | |||||
| 777 | .777 | read_this_file.txt | Lösegeld: 500 Dollar oder 1500 Dollar | XOR | Emsisoft Decrypter |
| 7ev3n | .R4A .R5A |
FILES_BACK.txt | Ändert das Desktop-Hintergrun |
7ev3n Decoder | |
| 7h9r | .7h9r | README_.TXT | 7h9r341@gmail.com | AES | |
| 7zipper | .7zipper | Saiba como recuperar seus arquivos.txt | zipper@email.tg | ||
| 8lock8 | .8lock8 | READ_IT.txt | Basiert auf HiddenTear | AES (256) | HT Bruteforcer |
| AAC Ransomware | .aac | Learn how to recover your files.txt | contatoaac@vpn.tg | ||
| AESMewLocker AESMew | .locked | READ_IT.txt | CONTACT_ME.AESMew@ |
AES | |
| AES_NI | .aes_ni .aes256 .aes_ni_0day |
!!! READ THIS - IMPORTANT !!!.txt | AES (256) | Avast Decryption Tool | |
| AiraCrop | ._AiraCropEncrypte |
How to decrypt your files.txt | |||
| Al-Namrood | .unavailable .disappeared |
How to decrypt your files.txt | Emsisoft Decrypter | ||
| Alcatraz Locker | .Alcatraz | ransomed.html | AES (256) + Base64 | Avast Decryption Tool | |
| Alfa Ransomware | .bin | README HOW TO DECRYPT | Vom Hersteller der Cerber-Ransomware | ||
| Alma Ransomware | Unlock_files_randomx |
AES (128) | |||
| Alpha Ransomware | .encrypt | Read Me (How Decrypt)! | Eine neue Version der TeslaCrypt-Ransomw |
AES (256) | Bleeping |
| Alphabet | Verschlüsselt keine Dateien / liefert Ihnen den Schlüssel | ||||
| AMBA | .amba .R5A |
READ_ (Russisch) | |||
| Amnesia | .amnesia .CRYPTBOSS .01 .02 |
HOW TO RECOVER ENCRYPTED FILES.TXT | s1an1er111@protonm |
Emsisoft Decrypter | |
| AnDROid | .android | Kaspersky Decrypter | |||
| Angela Merkel | .angelamerkel | ||||
| AngleWare | .AngleWare | READ_ME.txt | |||
| Angry Duck | .adk | Fordert 10 BTC | |||
| Annabelle | .ANNABELLE | AES (256) | Bitdefender Decrypt Tool | ||
| Anony | |||||
| Anti-DDos | .f*cked | Bleeping |
|||
| Anubis | .coded | Decryption Instructions.txt | EDA2 | AES (256) | |
| Apocalypse | .encrypted .SecureCrypted .FuckYourDat |
.How_To_Decrypt.txt | decryptionservice@ |
Emsisoft Decrypter | |
| ApocalypseVM | .encrypted .locked .FuckYourData .Encryptedfile .SecureCrypted |
.How_To_Get_Back.txt | Die Ransomware nutzt VMprotect | Emsisoft Decrypter | |
| ASN1 | !!!!!readme!!!!!.htm | ||||
| AtomSilo | .ATOMSILO | Avast AtomSilo Decryptor | |||
| Aura | Rakhni erstellt die Datei exit.hhr.oshit, die ein verschlüsseltes Kennwort enthält | Kaspersky Decrypter | |||
| Aurora | .aurora .animus .ONI .Nano .cryptoid .peekaboo .isolated .infected .locked .veracrypt .masked .crypton .coronolock .bukyak .serpom .systems32x |
Emsisoft Decrypter | |||
| AutoIt | Kaspersky Decrypter | ||||
| AutoLocky | .locky .locked |
info.txt info.html |
Programmiersprache AutoIt. Lösegeld: 0,75 Bitcoins | AES (128) | Emsisoft Decrypter |
| Avaddon | Lösegeldforderung per Bildschirmhintergr |
AES (256) + RSA (2048) | Emsisoft Decrypter | ||
| Aw3s0m3Sc0t7 | .enc | ||||
| BadBlock | Help Decrypt.html | Fügt verschlüsselten Dateien keine Erweiterung hinzu | RSA | Emsisoft Decrypter | |
| BadEncript | .bript | More.html | |||
| BaksoCrypt | .adr | Basiert auf my-Little-Ransomwa |
|||
| Bam-2021 | .bam! | Lösegeldforderung per Bildschirmhintergr |
AES & RSA | ||
| Bandarchor | Dateien werden teilweise verschlüsselt | AES (256) | Emsisoft Decrypter | ||
| BarRax | .BarRax | Basiert auf HiddenTear | BarRax Decryptor | ||
| Bart | .bart.zip | recover.txt recover.bmp |
AES (256) | Avast Decryption Tool | |
| BigBobRoss | .encryptedALL .djvu .obfuscated .cheetah |
Read Me.txt | RobSmithMba@proton |
AES (128) | Avast Decryption Tool |
| BitCryptor | .clf | Neue CoinVault Variante | Kaspersky Decrypter | ||
| BitKangaroo | .bitkangaroo | Bleeping |
|||
| BitStak | .bitstak | Bleeping |
|||
| BlackByte | .blackbyte | BlackByte_restoremyf |
Email: blackbyte@onionmai |
AES & RSA | |
| BlackShades Crypter | .Silent | Hacked_Read_me_to-de YourID.txt |
AES (256) | ||
| Blocatto | .blocatto | Basiert auf HiddenTear | AES (256) | ||
| Booyah | .bitstak | ||||
| Brazilian | .lock | MENSAGEM.txt | Basiert auf EDA2 | AES (256) | |
| Brazilian Globe | HOW_OPEN_FILES.html | ||||
| BrLock | .lock | AES | |||
| Browlock | .lock | keine lokale Verschlüsselung, gesperrter Browser | |||
| BTCWare | .btcware .cryptobyte .cryptowin .theva .onyon |
#_HOW_TO_FIX_!.hta | Verwandt mit / neue Version von CryptXXX | RC4 AES (192) |
Avast Decryption Tool |
| Bucbi | .lock | #_HOW_TO_FIX_!.hta | Ändert keine Dateinamen | GOST | |
| BuyUnlockCode | BUYUNLOCKCODE.txt | Löscht keine Schattenkopien | |||
| Calvo | .[seamoon@criptext |
info.txt info.hta |
cusapool@firemail. |
||
| Central Security Treatment Organization | .cry | !Recovery_[random_ch !Recovery_[random_ch |
|||
| Cerber 1 | .cerber | # DECRYPT MY FILES #.html # DECRYPT MY FILES #.txt # DECRYPT MY FILES #.vbs |
AES | Trend Micro File Decryptor | |
| Cerber 2 | .cerber2 | Spricht mit den Opfern und ändert das Desktop-Hintergrun |
|||
| Cerber 3 | .cerber3 | # HELP DECRYPT #.txt | Spricht mit den Opfern | ||
| CerberTear | |||||
| CheckMail7 | .checkmail7@proton |
Emsisoft Decrypter | |||
| Chernolocker | .CHERNOLOCKER .djvu .obfuscated .cheetah |
filelocker@protonm |
AES (256) | Emsisoft Decrypter | |
| Chimera | .crypt | YOUR_FILES_ARE_ENCRY YOUR_FILES_ARE_ENCRY |
Kaspersky Decrypter | ||
| CHIP | .CHIP .DALE |
CHIP_FILES.txt DALE_FILES.TXT |
|||
| ChupaCabra | .ChupaCabra | HowToDecrypt.txt | Verlangt ein Lösegeld von 0.003 - 0.02 BTC. Enthält eine Software zum Mining von Monero. | AES & RSA | |
| Click Me Game | |||||
| Clock | Verschlüsselt nichts | ||||
| CloudSword | Warning警告.html | ||||
| Cockblocker | .hannah | ||||
| CoinVault | .clf | wallpaper.jpg | Base64 + String Replacement | Kaspersky Decrypter | |
| Coms | .[golbnaty@aol.com |
FILES ENCRYPTED.txt | Basiert auf der Ransomware Dharma, golbnaty@aol.com | ||
| Coverton | .coverton .enigma .czvxce |
!!!-WARNING-!!!.html !!!-WARNING-!!!.txt |
AES (256) | ||
| CovidLocker | .covid .inprocess |
How_To_Recover.mht | undelivered@onet.p |
AES + RSA + ChaCha | |
| Creeper | .rag2hdst .creeper .cripper |
DECRIPT_Files.txt | Bezahlung per Monero
Mail-Adresse: skgrhk2118@tutanot |
AES (CBC) | |
| Crptxxx | .crptxxx | HOW_TO_FIX_!.txt | Verwendet den UAC-Bypass von @enigma0x3 | ||
| Cryaki | .{CRYPTENDBLACKDC} | Kaspersky Decrypter | |||
| Crybola | Kaspersky Decrypter | ||||
| CryFile | .criptiko .criptoko .criptokod .cripttt .aga |
SHTODELATVAM.txt Instructionaga.txt |
|||
| CryLocker | .cry | !Recovery_[random_ch !Recovery_[random_ch |
Identifiziert Opferstandorte mit der Google Maps API | ||
| CrypBoss | .crypt | Mail-Adresse: @dr.com | Emsisoft Decrypter | ||
| CrypMIC | README.TXT README.HTML README.BMP |
CryptXXX clone/spinoff | AES (256) | ||
| Crypt32 | AES (256) | Emsisoft Decrypter | |||
| Crypt38 | .crypt38 | AES | Bleeping |
||
| Crypt888 | Lock. | Lösegeldforderung per Bildschirmhintergr |
AES | Microcop Decryptor | |
| CryptConsole | How decrypt files.hta | Gibt sich als Globe Ransomware aus. Verschlüsselt die Dateien nicht. | CryptConsole Decrypter | ||
| Crypter | Verschlüsselt die Dateien nicht wirklich, sondern benennt sie lediglich um. | ||||
| CryptFIle2 | .CRYPTOSHIELD .rdmk .lesli .scl .code .rmd .rscl |
RSA | Avast Decryption Tool | ||
| CryptInfinite | .crinf | ReadDecryptFilesHere |
Emsisoft Decrypter | ||
| Crypto Ransomeware | |||||
| CryptoBit | .crinf | OKSOWATHAPPENDTOYOUR |
AES & RSA | ||
| CryptoBlock | RaaS | ||||
| CryptoDefense | .crinf | HOW_DECRYPT.TXT HOW_DECRYPT.HTML HOW_DECRYPT.URL |
Emsisoft Decrypter | ||
| CryptoDevil | .devil | ||||
| CryptoFinancial | |||||
| CryptoFortress | READ IF YOU WANT YOUR FILES BACK.html | Verschlüsselt 50% einer Datei. Maximale Dateigröße: 5 MB | AES (256) RSA (1024) |
||
| CryptoGraphic Locker | wallpaper.jpg | AES (128) | |||
| CryptoHasYou | .enc | YOUR_FILES_ARE_LOCKE |
Der Entschlüsselungs- |
AES (256) | |
| CryptoHost | Verbreitung per µ-Torrent-Client | AES (256) (RAR Implementierung) | Passwort Generator | ||
| CryptoJoker | README!!!.txt GetYouFiles.txt crjoker.html |
AES (256) | |||
| CryptoLocker | RSA (2048) | Kaspersky Decrypter | |||
| CryptoLocker 1.0.0 | |||||
| CryptoLocker 5.1 | |||||
| CryptoLuck / YafunnLocker | .[victim_id]_luck | @WARNING_FILES_ARE_E |
AES (256) | ||
| CryptoMix | HELP_YOUR_FILES.html (CryptXXX) HELP_YOUR_FILES.txt (CryptoWall 3.0, 4.0) |
RSA (2048) | Avast Decryption Tool | ||
| CryptON | .id-_locked .id-_locked_by_kre .id-_locked_by_per .id-_x3m .id-_r9oj .id-_garryweber@pr .id-_steaveiwalker .id-_julia.crown@i .id-_tom.cruz@indi .id-_CarlosBoltehe .id-_maria.lopez1@ |
RSA AES (256) SHA (256) |
Emsisoft Decrypter | ||
| Cryptorium | .ENC | Benennt Dateien nur um und verschlüsselt sie nicht | |||
| CryptoRoger | !Where_are_my_files! |
AES | |||
| CryptoShadow | .doomed | LEER_INMEDIATAMENTE. |
|||
| CryptoShield | .CRYPTOSHIELD .rdmk .lesli .scl .code .rmd .rscl .MOLE |
# RESTORING FILES #.HTML # RESTORING FILES #.TXT |
CryptoMix Variante | AES (256) ROT-13 |
Avast Decryption Tool |
| CryptoShocker | ATTENTION.url | AES | |||
| CryptoTor Locker2115 | HOW TO DECRYPT FILES.txt | AES | Decryption Anleitung | ||
| CryptoTrooper | AES | ||||
| CryptoWall 1 | DECRYPT_INSTRUCTION. DECRYPT_INSTRUCTION. DECRYPT_INSTRUCTION. INSTALL_TOR.URL |
||||
| CryptoWall 2 | HELP_DECRYPT.TXT HELP_DECRYPT.PNG HELP_DECRYPT.URL HELP_DECRYPT.HTML |
||||
| CryptoWall 3 | HELP_DECRYPT.TXT HELP_DECRYPT.PNG HELP_DECRYPT.URL HELP_DECRYPT.HTML |
||||
| CryptoWall 4 | HELP_YOUR_FILES.HTML HELP_YOUR_FILES.PNG |
||||
| CryptoWire | AES (256) | ||||
| CryptXXX | .crypt | de_crypt_readme.bmp de_crypt_readme.txt de_crypt_readme.html |
Kaspersky Decrypter | ||
| CryptXXX 2.0 | .crypt | personal-ID.txt personal-ID.html personal-ID.bmp |
Kaspersky Decrypter | ||
| CryptXXX 3.0 | .crypt .cryp1 .crypz .cryptz |
Kaspersky Decrypter | |||
| CryptXXX 3.1 | .cryp1 | Kaspersky Decrypter | |||
| CryPy | .cry | README_FOR_DECRYPT.t |
AES | ||
| CrySiS | .crysis .crypt .xtbl |
Eset CrySiS Decryptor | |||
| CTB-Faker | |||||
| CTB-Locker | .ctbl | AllFilesAreLocked-us DecryptAllFiles-user (random).html |
Zufällige Dateierweiterungen | RSA (2048) | |
| CTB-Locker WEB | AES (256) | ||||
| Cute Ransomware | .已加密 .encrypted |
Your files encrypted by our friends !!! .txt | Basiert auf my-Little-Ransomwa |
AES (128) | CuteRansomware Decryptor |
| Cyber SpLiTTer Vbs | Basiert auf HiddenTear | ||||
| Cyborg | .petra .EncryptedcFilePay .Cyborg1 .LockIt |
Cyborg_DECRYPT.txt | AES (256) | Emsisoft Decrypter | |
| Damage | .damage | Geschrieben in Delphi | SHA-1 Blowfish |
Emsisoft Decrypter | |
| Darkside | [victim's_ID].[fil |
README.[victim's_ID] |
Salsa20 | Bitdefender Decrypter | |
| Deadly for a Good Purpose | |||||
| Death Bitches | .locked | READ_IT.txt | |||
| DEDCryptor | .ded | Basiert auf EDA2 | AES (256) | ||
| Demo | .encrypted | HELP_YOUR_FILES.txt | Verschlüsselt nur .jpg-Dateien | ||
| Depsex | .Locked-by-Mafia | READ_ME.txt | Basiert auf HiddenTear | ||
| DeriaLock | .deria | unlock-everybody.txt | "Unlock All" Anleitung | ||
| DetoxCrypto | AES | ||||
| Dharma | .dharma .oral .urs wallet .zzzzz .adobe .c0v |
README.txt README.jpg Info.hta |
CrySiS Variante | Kaspersky Decrypter | |
| DirtyDecrypt | Emsisoft Decrypter | ||||
| DMALocker | cryptinfo.txt decrypting.txt start.txt |
Die verschlüsselten Dateien enthalten die folgenden Präfixe: Version 1: ABCXYZ11 Version 2: !DMALOCK Version 3: !DMALOCK3.0 Version 4: !DMALOCK4.0 | AES (256) Version 2-4 auch RSA |
Emsisoft Decrypter | |
| DMALocker 3.0 | AES (256) | Emsisoft Decrypter | |||
| DNRansomware | .fucked | Code zum entschlüsseln: 83KYG9NW-3K39V-2T3 |
|||
| Domino | .domino | README_TO_RECURE_YOU |
Basiert auf Hidden Tear | AES (256) | |
| Donald Trump | .ENCRYPTED | AES | |||
| DoNotChange | .id-7ES642406.cry .Do_not_change_the |
HOW TO DECODE FILES!!!.txt КАК РАСШИФРОВА |
AES (128) | ||
| DummyLocker | .dCrypt | ||||
| DXXD | .dxxd | ReadMe.TxT | Trend Micro File Decryptor | ||
| DynA-Crypt | .crypt | ||||
| EdgeLocker | .edgel | ||||
| EduCrypt | .isis .locked |
README.txt | Basiert auf Hidden Tear | ||
| EiTest | .crypted | ||||
| El-Polocker | .ha3 | qwer.html qwer2.html locked.bmp |
|||
| Encoder.xxxx | Instructions.html | Coded in GO | |||
| EncrypTile | Decrypt_[victim's_id Decrypt_[victim's_id Decrypt_[victim's_id How to buy bitcoin_[victim's_id |
deposithere@e-mail |
AES | Avast Decryption Tool | |
| encryptoJJS | .enc | How to recover.enc | |||
| Enigma | .enigma | enigma.hta enigma_encr.txt |
AES (128) | ||
| Enjey | Basiert auf RemindMe | ||||
| EnkripsiPC | .fucked | Das Verschlüsselungs- |
|||
| Erebus | README.HTML | AES | |||
| Everbe | .insane .DUESCRYPT .deuscrypt .Tornado .twist .everbe .embrace .pain .volcano |
Decrypter | |||
| Evil | .file0locked .evillock |
In Javascript programmiert | |||
| Exotic | .exotic | Verschlüsselt auch ausführbare Dateien | AES (128) | ||
| EyLamo Ransomware | READ_IT.txt | Verlangt ein Lösegeld von 0,5 BTC | AES | ||
| EZDZ Ransomware | .EZDZ .help .chch |
HELP_PC.EZDZ-REMOVE. READ_ME.TXT |
squadhack@email.tg | ||
| Fabiansomware | .encrypted | How_To_Decrypt.txt | Emsisoft Decrypter | ||
| FabSysCrypto | Basiert auf HiddenTear | ||||
| Fadesoft | |||||
| Fairware | Attackiert Linux O.S. | ||||
| Fakben | .locked | READ ME FOR DECRYPT.txt | Basiert auf Hidden Tear | ||
| Fake CryptoLocker | .cryptolocker | ||||
| FakeGlobe aka GlobeImposter | .crypt | HOW_OPEN_FILES.hta | Emsisoft Decrypter | ||
| Fantom | .fantom .comrade |
DECRYPT_YOUR_FILES.H RESTORE-FILES![id] |
Basiert auf EDA2 | AES (128) | |
| FenixLocker | .FenixIloveyou!! | Help to decrypt.txt | Emsisoft Decrypter | ||
| FILE FROZR | RaaS | ||||
| FileLocker | .ENCR | ||||
| FindZip | .crypt | DECRYPT.txt HOW_TO_DECRYPT.txt README.txt |
Avast Decryption Tool | ||
| FireCrypt | .firecrypt | [random_chars]-READ_ |
AES (256) | ||
| Flyper | .locked | Basiert auf EDA2 / HiddenTear | |||
| Fonco | Mailkontakt: safefiles32@mail.r |
||||
| FortuneCookie | |||||
| Free-Freedom | .madebyadam | Code zur Entschlüsselung lautet: adam or adamdude9 | |||
| FSociety | .fs0ciety .dll |
fs0ciety.html DECRYPT_YOUR_FILES.H |
Basiert auf EDA2 und auf RemindMe | ||
| Fury | Kaspersky Decrypter | ||||
| GandCrab | .GDCB .CRAB .KRAB .%RandomLetters% |
GDCB-DECRYPT.txt CRAB-DECRYPT.txt KRAB_DECRYPT.txt %RandomLetters%-DECR %RandomLetters%-MANU |
Avast Decryption Tool | ||
| Geneve | DECRYPT.html | Zufällige Dateiendung | AES (256) RSA (2048) |
||
| GetCrypt | # DECRYPT MY FILES #.txt | Hängt eine zufällige 4-Zeichen-Erweiter |
Emsisoft Decrypter | ||
| GhostCrypt | .Z81928819 | AES (256) | Bleeping |
||
| Gingerbread | |||||
| Globe v1 | .purge | How to restore files.hta | Blowfish | Trend Micro File Decryptor | |
| Globe v2 | .lovewindows .openforyou@india. |
Blowfish | Trend Micro File Decryptor | ||
| Globe v3 | .[random].blt .[random].encrypte .[random].raid10 .[mia.kokers@aol.c .[random].globe .unlockvt@india.co .rescuers@india.co .lock .locked .decrypt2017 .hnumkhotep |
RC4 AES (256) |
Emsisoft Decrypter | ||
| GNL Locker | .locked | UNLOCK_FILES_INSTRUC |
AES (256) | ||
| GOG | .L0CKED | DecryptFile.txt | |||
| Gomasom | .crypt | Mail-Adresse im Dateinamen | Emsisoft Decrypter | ||
| Goopic | Your files have been crypted.html | ||||
| Gopher | OS X ransomware (PoC) | ||||
| Gremit | .rnsmwr | ||||
| Guster | .locked | ||||
| Hacked | .encrypted .payrmts .locked .Locked |
Jigsaw Ransomware Variante | |||
| Hakbit | AES (256) | Emsisoft Decrypter | |||
| HappyDayzz | 3DES AES (128) AES (192) AES (256) DES RC2 RC4 |
||||
| Harasom | Emsisoft Decrypter | ||||
| HDDCryptor | Verwendet diskcryptor.net für die vollständige Festplatten-Versch |
||||
| Heimdall | File marker: Heimdall--- | AES (128) CBC |
|||
| Help_dcfile | .XXX | help_dcfile.txt | |||
| Herbst | .herbst | ||||
| Hermes | DECRYPT_INFORMATION. UNIQUE_ID_DO_NOT_REM |
AES | |||
| Hi Buddy! | .cry | AES (256) | |||
| HiddenTear | .locked .34xxx .bloccato .BUGSECCCC .Hollycrypt .lock .saeid .unlockit .razy .mecpt .monstro .lok .암호화됨 .8lock8 .fucked .flyper .kratos .drypted .CAZZO .doomed |
READ_IT.txt MSG_FROM_SITULA.txt DECRYPT_YOUR_FILES.H |
AES (256) | Avast Decryption Tool | |
| HimalayA | * no data *. | E-Mail: himalayaraas@dnmx. |
AES (256) | ||
| Hitler | Löscht Dateien | ||||
| HKCrypt | .hacked | @readme_English.txt How_to_decrypt_files |
RSA (4096) | Emsisoft Decrypter | |
| HolyCrypt | AES | ||||
| HTCryptor | Enthält eine Funktion zur Deaktivierung der Windows-Firewall | ||||
| Hucky | .locky | _Adatok_visszaallita _locky_recover_instr |
Basiert auf Locky | AES RSA |
|
| HydraCrypt | README_DECRYPT_HYRDA |
CrypBoss Familie | Emsisoft Decrypter | ||
| IFN643 | |||||
| iLock | |||||
| iLockLight | .crime | ||||
| ImS00rry | README | Das Opfer wird gebeten, die Kriminellen über Telegramm (@Ims00rybot) zu kontaktieren. Fügt keine Erweiterung hinzu. | AES (128) | Emsisoft Decrypter | |
| Imshifau | .imshifau | INFO OF DECRYPT.TXT | Mail-Adressen: Imshifau@vegeta.cy |
AES (256) RSA |
|
| InsaneCrypt | .[everbe@airmail.c .everbe .embrace .pain |
!=How_recovery_files |
Everbe Decryptor | ||
| International Police Association | %Temp%-random-.bmp | Bleeping |
|||
| iRansom | .Locked | ||||
| Jack.Pot | |||||
| JagerDecryptor | !ENC | Important_Read_Me.ht |
Dateinamen werden vorangestellt | ||
| JapanLocker | |||||
| JavaLocker | .javalocker | DES | Emsisoft Decrypter | ||
| JCrypt | .jcrypt .locked .daddycrypt .omero .ncovid |
___ RECOVER__FILES __. Jcrypt.txt ___ RECOVER__FILES __. Daddycrypt.txt ___ RECOVER__FILES __. Omero.txt ___ RECOVER__FILES __. Ncovid.txt ___ RECOVER__FILES __. Crypted.txt ___ RECOVER__FILES __. Iam_watching.txt |
this.email.address |
AES + RSA | |
| Jeiphoos | |||||
| Jhon Woddy | .killedXXX | Der selbe Code wie bei der der DNRansomware. Sperrbildschirm-Ke |
Bleeping |
||
| Jigsaw | .kkk .btc .gws .J .encrypted .porno .payransom .pornoransom .epic .xyz .encrypted .payb .payb .pays .payms .paymds ,paymts .payrms .payrmts .paymrts .paybtcs .fun .hush .uk-dealer@sigaint .fucked |
AES (256) | Avast Decryption Tool | ||
| Job Crypter | .locked .css |
Comment débloquer mes fichiers.txt Readme.txt |
3DES | ||
| JohnyCryptor | |||||
| Juicy Lemon | .id-{number}_maest |
Juicy Lemon Decryptor | |||
| Kaandsona | .kencf | ||||
| Kangaroo | .crypted_file | filename.Instruction |
Von den Entwicklern hinter der Apokalypse Ransomware, Fabiansomware und Esmeralda | ||
| Karma | .karma | # DECRYPT MY FILES #.html # DECRYPT MY FILES #.txt |
Gibt vor, das Windows-Programm Windows-TuneUp zu sein | AES | |
| Karmen | .grt | RaaS, basiert auf HiddenTear | |||
| Kasiski | .[KASISKI] | INSTRUCCIONES.txt | |||
| KawaiiLocker | How Decrypt Files.txt | Kawaii Decrypter | |||
| KeRanger | .encrypted | OS X Ransomware | AES | Anleitung | |
| KeyBTC | keybtc@inbox_com | DECRYPT_YOUR_FILES.t READ.txt readme.txt |
Emsisoft Decrypter | ||
| KEYHolder | how_decrypt.gif how_decrypt.html |
tuyuljahat@hotmail |
|||
| KillDisk | AES (256) | ||||
| KillerLocker | .rip | Möglicherweise ein portugiesischer Entwickler | |||
| KimcilWare | .kimcilware .locked |
Infiziert Webseiten | AES | ||
| Kirk | .Kirked | RANSOM_NOTE.txt | Bezahlung in Monero | ||
| KokoKrypt | .kokolocker | AES (256) | Emsisoft Decrypter | ||
| Koolova | Italienischer Text, der es nur auf den Ordner "Test" auf dem Desktop des Benutzers abzielt | ||||
| Korean | .암호화됨 | ReadMe.txt | Basiert auf HiddenTear | AES (256) | |
| Kostya | .kostya | ||||
| Kozy.Jozy | .31392E30362E32303 |
w.jpg | RSA (2048) | ||
| Kraken | .kraken | _HELP_YOUR_FILES.htm |
|||
| KratosCrypt | .kratos | README_ALL.html | |||
| KRider | .kr3 | ||||
| KryptoLocker | KryptoLocker_README. |
AES (256) | |||
| LambdaLocker | .lambda_l0cked .MyChemicalRomance |
READ_IT.hTmL | Python Ransomware | AES (256) | Avast Decryption Tool |
| LanRan | @__help__@ | Variante der Open-Source Ransomware MyLittleRansomware | |||
| LeChiffre | .LeChiffre | How to decrypt LeChiffre files.html | Mail-Adresse: decrypt.my.files@g |
Emsisoft Decrypter | |
| Legion | ._23-06-2016-20-27 .$centurion_legion |
Ändert das Desktop-Hintergrun |
Avast Decryption Tool | ||
| Lick | .Licked | RANSOM_NOTE.txt | Variant of Kirk | ||
| Linux.Encoder | Linux Ransomware | Bitdefender Anleitung | |||
| LK Encryption | Basiert auf HiddenTear | ||||
| LLTP Locker | .ENCRYPTED_BY_LLTP .ENCRYPTED_BY_LLTP |
LEAME.txt | Zielgruppe: Spanisch sprechende Opfer | AES (256) | |
| Lock93 | .lock93 | ||||
| Lockbit | .lockbit | Restore-My-Files.txt | |||
| LockCrypt | .lock | ReadMe.TxT | |||
| Locked-In | RESTORE_CORUPTED_FIL |
Basiert auf RemindMe | Anleitung | ||
| Locker | Ändert den Dateityp nicht | Locker Unlocker | |||
| LockerAdmin | .$$$ | readme.txt | AES | ||
| LockFile | .lockfile | Avast AtomSilo Decryptor | |||
| LockLock | .locklock | READ_ME.TXT | AES (256) | ||
| Locky | .locky .zepto |
_Locky_recover_instr _Locky_recover_instr _HELP_instructions.t _HELP_instructions.b |
AES (128) | ||
| Lomix | Basiert auf die Open-Source Ransomware CryptoWire | ||||
| Lortok | .crime | ||||
| LowLevel04 | oor. | ||||
| M4N1F3STO | Verschlüsselt nicht. Freischaltcode: suckmydicknigga | ||||
| Mabouia | OS X ransomware (PoC) | ||||
| MacAndChess | Basiert auf HiddenTear | ||||
| Magic | .magic | DECRYPT_ReadMe1.TXT DECRYPT_ReadMe.TXT |
Basiert auf EDA2 | AES (256) | |
| MaktubLocker | _DECRYPT_INFO_[ext |
AES (256) RSA (2048) |
|||
| Mammon | .[mammon0503@tutan |
readme-warning.txt | mammon0503@tutanot |
||
| Marlboro | .oops | _HELP_Recover_Files_ |
XOR | Emsisoft Decrypter | |
| MarsJoke | .a19 .ap19 |
!!! Readme For Decrypt !!!.txt ReadMeFilesDecrypt!! |
Kaspersky Anleitung | ||
| MasterBuster | CreatesReadThisFileI |
||||
| Matrix | [5 numbers]-MATRIX-READ |
GnuPG | |||
| McBurglar | .mcburglar | README-MCBURGLAR.txt | AES & RS | ||
| Meister | Hat Französische Nutzer im Visier | ||||
| Merry X-Mas! | .PEGS1 .MRCR1 .RARE1 .MERRY .RMCM1 |
YOUR_FILES_ARE_DEAD. MERRY_I_LOVE_YOU_BRU |
Geschrieben in Delphi | Emsisoft Decrypter | |
| Meteoritan | where_are_your_files readme_your_files_ha |
||||
| MIRCOP | Lock. | Lösegeldforderung per Bildschirmhintergrun |
Microcop Decryptor | ||
| MireWare | .fucked .fuck |
READ_IT.txt | AES (256) | ||
| Mischa | .3P7m .arpT .eQTz .3RNu |
YOUR_FILES_ARE_ENCRY YOUR_FILES_ARE_ENCRY |
|||
| MM Locker | .locked | READ_IT.txt | AES (256) | ||
| Mobef | .KEYZ .KEYH0LES |
4-14-2116-INFECTION. IMPORTANT.README |
|||
| Mole | .mole .mole02 |
INSTRUCTION_FOR_HELP |
Mole02 Decryptor | ||
| Monument | |||||
| MOTD | .enc | motd.txt | |||
| MSN CryptoLocker | RESTORE_YOUR_FILES.t |
||||
| N-Splitter | .кибер разветвит |
Russische Koolova-Variante | |||
| n1n1n1 | decrypt explanations.html | Filemaker: "333333333333" | |||
| Nagini | |||||
| NanoLocker | ATTENTION.RTF | Ändert den Dateityp nicht | AES (256) RSA |
NanoLocker Decrypter | |
| Nefilim | .BENTLEY .NEFILIM |
NEFILIM-DECRYPT.txt BENTLEY-HELP.txt |
E-Mail Adressen: jamesgonzaleswork1 |
AES (128) RSA (2048) |
|
| Nemucod | .crypted | Decrypted.txt | 7zip (a0.exe)-Variante kann nicht entschlüsselt werden. Verschlüsselt die ersten 2048 Bytes | XOR(255) 7zip |
Emsisoft Decrypter |
| Netix | AES (256) | ||||
| New Zeoticus 2.0 | .pandora [random_string].ou |
pandoraREADME.html README.html |
Ändert den Desktophintergrund |
||
| Nhtnwcuf | !_RECOVERY_HELP_!.tx HELP_ME_PLEASE.txt |
Verschlüsselt die Dateien nicht. Die Dateien werden zerstört | |||
| Nitro Ransomware | .givemenitro | Das Hintergrundbild ändert sich und zeigt ein wütendes Discord-Logo. Fordert einen Discord Nitro-Geschenkcode |
|||
| NMoreira | .maktub .__AiraCropEncrypt .aac |
Recupere seus arquivos. Leia-me!.txt Learn how to recover your files.txt |
RSA AES (256) |
Emsisoft Decrypter | |
| NoobCrypt | ransomed.html | Avast Decryption Tool | |||
| Nuke | .nuclear55 | !!_RECOVERY_instruct !!_RECOVERY_instruct |
AES | ||
| Nullbyte | _nullbyte | Bleeping |
|||
| Ocelot | Verschlüsselt nichts | ||||
| ODCODC | .odcodc | XOR | Bleeping |
||
| Offline ransomware | .cbf | desk.bmp desk.jpg |
.777 E-Mail Adresse | Kaspersky Decrypter | |
| OMG! Ransomware | .LOL! .OMG! |
how to get data.txt | |||
| Onyx | Georgische Ransomware | ||||
| Operation Global III | Decryption Tool | ||||
| Owl | dummy_file.encrypt |
log.txt | |||
| OzozaLocker | .Locked | HOW TO DECRYPT YOU FILES.txt | Emsisoft Decrypter | ||
| PadCrypt | .padcrypt | IMPORTANT READ ME.txt File Decrypt Help.html |
Enthält einen Live Support Chat | ||
| Padlock Screenlocker | Ensperr-Code: ajVr/G\RJz0R | ||||
| Paradise | .paradise2ksys19 .p3rf0rm4 .FC .CORP .STUB |
Salsa 20 RSA (1024) |
Emsisoft Decrypter | ||
| Pashka | .pashka | HELP_ME_RECOVER_MY_F |
AES | ||
| Patcher | .crypt | README!.txt | Ausgerichtet auf MacOS-Benutzer | Anleitung | |
| PayDay | .sexy | !!!!!ATENÇÃO!!!!!. |
Basiert auf Hidden-Tear | ||
| PayDOS | Batch-Datei Passcode: AES1014DW256 | ||||
| Paysafecard Generator 2016 | .cry_ | ||||
| PClock | Your files are locked !.txt Your files are locked !!.txt Your files are locked !!!.txt Your files are locked !!!!.txt |
CryptoLocker-Nacha |
XOR | Emsisoft Decrypter | |
| PetrWrap | |||||
| Petya | Sperrt den kompletten Computer | Passwort Decrypter | |||
| Philadelphia | .locked | Programmiert von "The_Rainmaker" | AES (256) | Emsisoft Decrypter | |
| Phobos | .phobos | Überarbeitete Dharma Ransomware | |||
| Phoenix | .R.i.P | Important!.txt | Basiert auf HiddenTear | ||
| Pickles | .EnCrYpTeD | READ_ME_TO_DECRYPT.t |
Python Ransomware | ||
| PizzaCrypts | .id-[victim_id]-ma |
Bleeping |
|||
| PokemonGO | .locked | Basiert auf Hidden Tear | AES (256) | ||
| Polyglot | Imitiert den CTB-Locker | AES (256) | Kaspersky Decrypter | ||
| Popcorn Time | .filock | restore_your_files.h restore_your_files.t |
AES (256) | ||
| Potato | .potato | README.png README.html |
AES (256) | ||
| PowerWare | Bleeping |
||||
| PowerWorm | DECRYPT_INSTRUCTION. |
Sieht aus wie CryptoWall 3. Jedoch mit zusätzlichen Warnungen am unteren Rand, u. a. dass der Lösegeldpreis nach einiger Zeit steigen wird. Keine Entschlüsselung möglich! Die Ransomware löscht die Schlüssel und vernichtet die Dateien. | |||
| Princess Locker | !_HOW_TO_RESTORE_[ex !_HOW_TO_RESTORE_[ex !_HOW_TO_RESTORE_*id .*id* @_USE_TO_FIX_JJnY.tx |
Princess Locker Decryptor | |||
| PRISM | |||||
| Project34 | ПАРОЛЬ.txt | ||||
| ProposalCrypt | .crypted | Proposal Crypt Decrypter | |||
| Ps2exe | |||||
| PyL33T | .d4nk | Python Ransomware | |||
| Pylocky | RANSOM_PYLOCKY.A | PyLocky Decryptor | |||
| R | Ransomware.txt | ||||
| R980 | .crypt | DECRYPTION INSTRUCTIONS.txt rtext.txt |
|||
| RAA encryptor | .locked | !!!README!!![id].rtf | |||
| Rabion | RaaS-Kopie von Ranion RaaS | ||||
| Radamant | .RDM .RRK .RAD .RADAMANT |
YOUR_FILES.url | AES (256) | Emsisoft Decrypter | |
| Rakhni | .locked .kraken .darkness .nochance .oshit .oplata@qq_com .relock@qq_com .crypto .helpdecrypt@ukr.n .pizda@qq_com .dyatel@qq_com _ryp .nalog@qq_com .chifrator@qq_com .gruzin@qq_com .troyancoder@qq_co .encrypted .cry .AES256 .enc .hb15 |
fud.bmp paycrypt.bmp strongcrypt.bmp maxcrypt.bmp Random.bmp |
Dateien können teilweise verschlüsselt sein | Kaspersky Decrypter | |
| Ramsomeer | Basiert auf DUMB | ||||
| Ranion | RaaS Service | AES (256) | |||
| Rannoh | Kaspersky Decrypter | ||||
| RanRan | .zXz | VictemKey_0_5 VictemKey_5_30 VictemKey_30_100 VictemKey_100_300 VictemKey_300_700 VictemKey_700_2000 VictemKey_2000_3000 VictemKey_3000 zXz.html |
RanRan Decryption | ||
| Ransoc | Verschlüsselt keine Benutzerdateien | ||||
| Ransom32 | |||||
| Ransomwared | .ransomwared | DES | Emsisoft Decrypter | ||
| Rector | .vscrypt .infected .bloc .korrektor |
Kaspersky Decrypter | |||
| RedRum | .id-.[].redrum | decryption.txt | RSA (1024) | Emsisoft Decrypter | |
| RemindMe | .remind | decypt_your_files.ht |
|||
| Rokku | .rokku | README_HOW_TO_UNLOCK README_HOW_TO_UNLOCK |
Curve (25519) + ChaCha | ||
| Samas-Samsam | .encryptedAES .encryptedRSA .encedRSA .justbtcwillhelpyo .btcbtcbtc .btc-help-you .only-we_can-help_ .iwanthelpuuu |
HELP_DECRYPT_YOUR_FI |
AES (256) RSA (2096) |
Bleeping |
|
| Sanction | .sanction | DECRYPT_YOUR_FILES.H |
AES (256) RSA (2096) |
||
| Sanctions | .wallet | RESTORE_ALL_DATA.htm |
AES (256) RSA (2048) |
||
| Sardoninir | .enc | ||||
| Satan | .stn | HELP_DECRYPT_FILES.h |
RaaS | AES (256) RSA (2096) |
|
| Satana | Sarah_G@ausi.com__ |
!satana!.txt | |||
| Scraper | Ändert den Dateityp nicht | Scraper Decryptor | |||
| SerbRansom | .velikasrbija | ||||
| Serpent | .serpent | HOW_TO_DECRYPT_YOUR_ HOW_TO_DECRYPT_YOUR_ |
Batch-Datei Passcode: RSA1014DJW2048 | AES (256) | |
| Serpico | DetoxCrypto Variante | AES | |||
| Shade (Troldesh) | xtbl ytbl breaking_bad heisenberg better_call_saul los_pollos da_vinci_code magic_software_syn windows10 windows8 no_more_ransom tyson crypted000007 crypted000078 rsa3072 decrypt_it dexter miami_california. |
README{1-10}.txt | AES (256) | Kaspersky Decrypter | |
| Shark | .locked | Readme.txt | AES (256) | ||
| ShellLocker | .L0cked | ||||
| ShinoLocker | .shino | ||||
| Shujin | 文件解密帮助.t |
||||
| Simple_Encoder | .~ | _RECOVER_INSTRUCTION |
AES | ||
| SkidLocker / Pompous | .locked | READ_IT.txt | AES (256) | Decryption Anleitung | |
| SkyName | Basiert auf HiddenTear | ||||
| Smash! | |||||
| Smrss32 | .encrypted | _HOW_TO_Decrypt.bmp | |||
| SNSLocker | .RSNSlocked .RSplited |
READ_Me.txt | AES (256) | ||
| Somik1 | .somik1 .arnoldmichel2 @ tutanota.com |
WARNING.txt WARNING2.txt WARNING3.txt |
AES | ||
| SpartCrypt | .SpartCrypt[LordCrac .CoronaCrypt[u.conta |
Emsisoft Decrypter | |||
| Spider | .Spider | AES | |||
| SplinterJoke | .SplinterJoke | ransom_note.txt | AES & RSA | ||
| Spora | [Infection-ID].HTM |
||||
| Sport | .sport | ||||
| Stampado | .locked | Zufällige Nachricht enthält eine Bitcoin-Adresse mit Anweisungen. Coded by "The_Rainmaker". Löscht zufällig alle 6 Stunden eine Datei und löscht nach 96 Stunden den Entschlüsselung |
AES (256) | Decryption Anleitung | |
| STOP Djvu | .pcqq .igvm |
_readme.txt | helpmanager@airmai |
Emsisoft Decrypter | |
| Strictor | .locked | AES (256) | |||
| StrikedRansomware | .Andrey.gorlachev@ .nukem@mortalkomba .rap@mortalkombat. .m.pirat@aol.com .duk@mortalkombat. .jekabro@mortalkom .bitcoin@mortalkom |
Bleeping |
|||
| Surprise | .surprise .tzu |
DECRYPTION_HOWTO.Not |
AES (256) | ||
| Survey | ThxForYurTyme.txt | ||||
| SynAck | RESTORE_INFO-[ID].tx |
synack@secmail.pro
synack@scryptmail. |
ECIES + AES (256), RSA (2048) + AES (256) | Emsisoft Decrypter | |
| SynoLocker | |||||
| SZFLocker | .szf | AVG Decryptor | |||
| TaRRaK | .TaRRaK | Note_fom_TaRRaK.txt | XXTEA | ||
| TeamXrat | .___xratteamLucked | Como descriptografar os seus arquivos.txt | AES (256) | ||
| TeleCrypt | .xcri | Telecrypt erzeugt eine zufällige Zeichenfolge, die zwischen 10 und 20 Zeichen lang ist und nur die Buchstaben vo,pr,bm,xu,zt,dq enthält. | TeleCrypt Decrypter | ||
| TeslaCrypt 3.0+ | .micro .xxx .ttt .mp3 |
AES (256) ECHD SHA1 |
ESET Decryptor | ||
| TeslaCrypt0+ | .vvv .ecc .exx .ezz .abc .aaa .zzz .xyz |
HELP_TO_SAVE_FILES.t Howto_RESTORE_FILES. |
TeslaCrypt Decryptor | ||
| Thanatos | .THANATOS | AES (256) | Thanatos Decryptor | ||
| Thanksgiving | |||||
| Threat Finder | HELP_DECRYPT.HTML | ||||
| TorrentLocker | .Encrypted .enc |
HOW_TO_RESTORE_FILES DECRYPT_INSTRUCTIONS DESIFROVANI_POKYNY.h INSTRUCCIONES_DESCIF ISTRUZIONI_DECRITTAZ ENTSCHLUSSELN_HINWEI ONTSLEUTELINGS_INSTR INSTRUCTIONS_DE_DECR SIFRE_COZME_TALIMATI wie_zum_Wiederherste |
AES (256) | Decryption Anleitung | |
| TowerWeb | Payment_Instructions |
||||
| Toxcrypt | .toxcrypt | tox.html | |||
| Troldesh | .better_call_saul .xtbl .da_vinci_code .windows10 |
READMEnumber.txt | AES (256) | ||
| TrueCrypter | .enc | AES (256) | |||
| Trump Locker | .TheTrumpLockerf .TheTrumpLockerfp |
What happen to my files.txt | |||
| Turkish | .sifreli | ||||
| Turkish (Fake CTB-Locker) | .encrypted | Beni Oku.txt | keys in '%name%.manifest.x |
||
| Turkish Ransom | .locked | DOSYALARINIZA ULAŞMAK İÇİN AÇINIZ.html | AES (256) | ||
| TurkStatik | .ciphered | Emsisoft Decrypter | |||
| UltraLocker | Basiert auf der Open-Source-Ransom |
AES (256) | |||
| UmbreCrypt | .umbrecrypt | Emsisoft Decrypter | |||
| UnblockUPC | Files encrypted.txt | ||||
| Ungluk | .H3LL .0x0 .1999 |
READTHISNOW!!!.txt Hellothere.txt YOUGOTHACKED.TXT |
Die Opfer sollen per Bitmessage Kontakt zum Betrüger aufnehmen | AES | |
| Unlock26 | .locked-[XXX] | ReadMe-XXX.html | |||
| Unlock92 | .CRRRT .CCCRRRPPP |
||||
| Vanguard | GO Ransomware | ||||
| VapeLauncher | CryptoWire Variante | ||||
| VaultCrypt | .vault .xort .trun |
VAULT.txt xort.txt trun.txt random.hta |
Benutzt eine gpg.exe | ||
| VBRANSOM 7 | .VBRANSOM | Verschlüsselt nicht wirklich | |||
| Venis Ransomware | VenisRansom@proton |
||||
| VenusLocker | .Venusf .Venusp |
ReadMe.txt | Basiert auf EDA2 | AES (256) | |
| VietnamPav | .encrypted | How to restore files.hta | Mail: zitenmax@rambler.r |
||
| Virlock | |||||
| Virus-Encoder | .CrySiS .xtbl |
How to decrypt your data.txt | AES (256) | ||
| Vortex | .aes | ||||
| vxLock | .vxLock | ||||
| WannaCry | .wcry .wncry .WNCRY .WCRY |
@Please_Read_Me@.txt | |||
| WildFire Locker | .wflx | HOW_TO_UNLOCK_FILES_ |
Kaspersky Decrypter | ||
| Winnix Cryptor | .wnx | YOUR FILES ARE ENCRYPTED!.txt | GPG | ||
| XCrypt | Xhelp.jpg | ||||
| XData | .~xdata~ | HOW_CAN_I_DECRYPT_MY |
Avast Decryption Tool | ||
| Xorist | .EnCiPhErEd .73i87A .p5tkjw .PoAr2w .fileiscryptedhard .0JELvV .6FKR8d .UslJ6m .n1wLp0 .5vypSa |
HOW TO DECRYPT FILES.TXT | XOR TEA |
Kaspersky Decrypter | |
| XRTN | .xrtn | VaultCrypt Familie | |||
| XYZconfig | .xyz | _Readme_.txt | Fordert 100-150 XMR (Monero) juanjoorodriguez@p juanjo.rodriguez@t |
||
| XYZWare | Basiert auf HiddenTear | ||||
| You Have Been Hacked!!! | .Locked | Versucht Passwörter zu stehlen | |||
| YourRansom | .yourransom | README.txt | |||
| Zcrypt | .zcrypt | ||||
| Zeta | .CRYPTOSHIELD .rdmk .lesli .scl .code .rmd .rscl |
# HELP_DECRYPT_YOUR_FI |
AES (256) | Avast Decryption Tool | |
| Zimbra | .crypto | how.txt | mpritsken@priest.c |
||
| ZinoCrypt | .ZINO | ZINO_NOTE.TXT | |||
| Zlader / Russian | .vault | VaultCrypt Familie | RSA | ||
| Zorab | .ZRB | AES (256) | Emsisoft Decrypter | ||
| Zorro | .zorro | Take_Seriously (Your saving grace).txt | |||
| zScreenLocker | |||||
| Zyka | .locked | Bleeping |
|||
| Zyklon | .zyklon |
Ransomware not found?
Alternatively you can use the ID Ransomware service to find out which ransomware has infected your computer. To do that you need to upload the ransom note and an encrypted file of the ransomware. If available, you will be provided with links to decryption tools.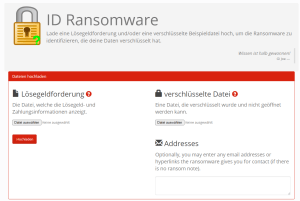
You can also find decryption tools on the NoMoreRansom.org website from the Dutch police, Europol, Intel Security as well as Kaspersky Lab.
Decryptor / Entschlüsselungstools
Avast Decryption Tool

AES_NI, Alcatraz Locker, ApocalypseVM, BadBlock, Bart, BigBobRoss, BTCWare, CryptFIle2, CryptoMix, CryptoShield, HiddenTear, EncrypTile, FindZip, GandCrab, Jigsaw, LambdaLocker, Legion, NoobCrypt, XData, Zeta.
↑ Go to top
Bleepingcomputer Decrypter

Alpha Ransomware (Alpha
Zum Download-Center von Bleepingcomputer: https://www.bleepingcomputer.com/download/windows/ransomware-decryptors/
↑ Go to top
Emsisoft Decrypter

777, Al-Namrood, Amnesia, Apocalypse, ApocalypseVM, Aurora, AutoLocky, Avaddon, BadBlock, Bandarchor, CheckMail7, CrypBoss, Crypt32, CryptInfinite, CryptoDefense, CryptON, Cyborg, Damage, DirtyDecrypt, DMALocker, DMALocker 3.0, Fabiansomware, FakeGlobe aka GlobeImposter, FenixLocker, Globe v3, Gomasom, GetCrypt, Hakbit, Harasom, HKCrypt, HydraCrypt, ImS00rry, JavaLocker, KeyBTC, KokoKrypt, LeChiffre, Marlboro, Merry X-Mas!, Nemucod, NMoreira, OzozaLocker, Paradise, PClock, Philadelphia, Radamant, Ransomwared, RedRum, SpartCrypt, STOP Djvu, SynAck, TurkStatik, UmbreCrypt, Zorab.
↑ Go to top
Kaspersky Decrypter

BitCryptor, CoinVault, Cryaki, Crybola, CryptoLocker, CryptXXX, CryptXXX 2.0, CryptXXX 3.0, CryptXXX 3.1, Dharma, Fury, MarsJoke, Offline ransomware, Polyglot, Rakhni, Rannoh, Rector, Shade (Troldesh), WildFire Locker, Xorist.
Download: https://noransom.kaspersky.com/
↑ Go to top
Trend Micro File Decryptor

AutoLocky, Cerber 1, DXXD, Globe v1, Globe v2.
↑ Go to top
 Felix Bauer
Felix Bauer René Hifinger
René Hifinger